🔒 The math behind unbreakable codes - and the puzzles that bring it to life. 🔒
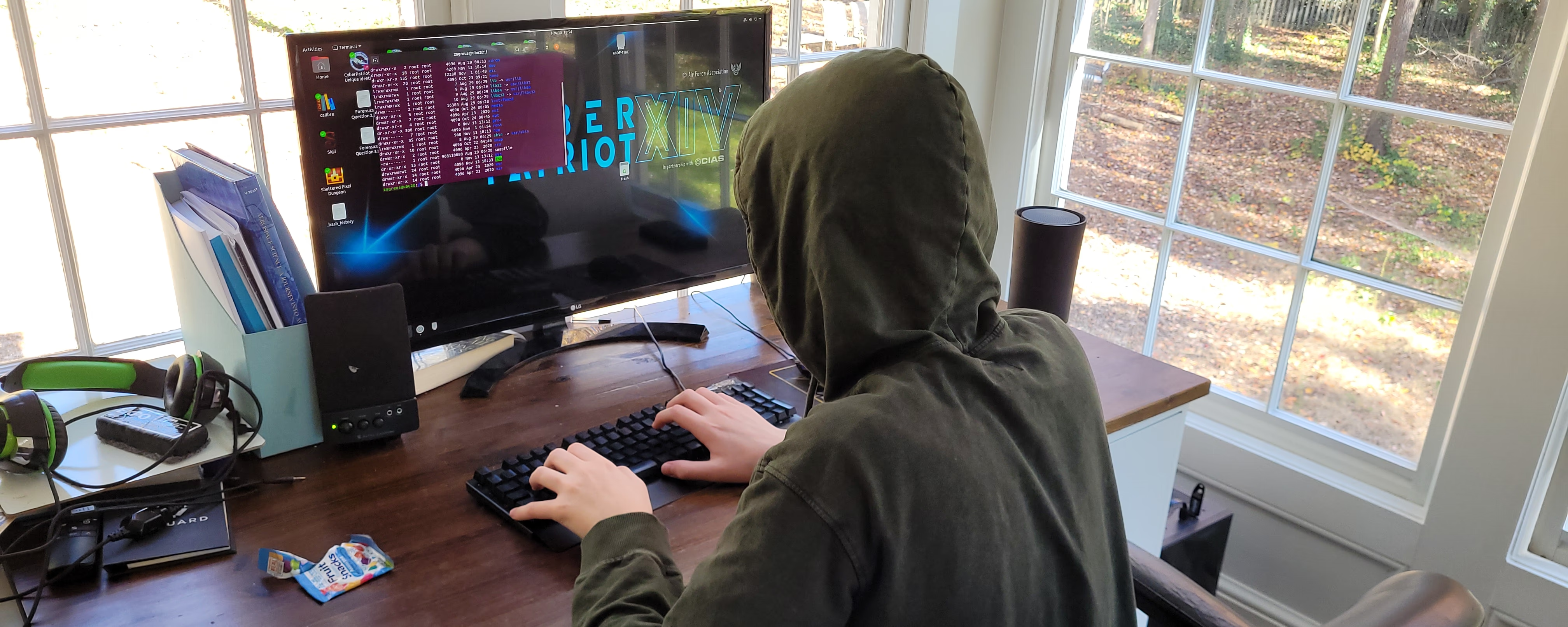
Capture-the-Flag, exponential password space, and Blue Team thinking from day one.
About This Workshop
Much of cybersecurity and nearly all of cryptography is a numbers game - math with numbers so large that computers can't manage them. Students explore those numbers at a scale they can see, watching them grow into territory no one can brute-force. They also poke at pre-built Capture-the-Flag puzzles and run a few eye-popping demos that feel like elite hacker moves while being completely benign. Nothing we do puts any computer or network at risk before, during, or after this session.
What Students Will Do
- 🔢 Work the Exponents - A 4-character password has some number of values. An 8-character one has way more, not twice as many. Compute the actual numbers and feel them grow
- 🎯 Probability Games - A locked phone has a 4-digit PIN. A thief tries 1000 random PINs - what's the chance they get in? Now do 6 digits
- 😀 Compare Passwords Honestly - Short with symbols vs. long all-lowercase: which is actually harder to crack? Run the math
- 🏁 Capture-the-Flag - Pre-built puzzles with hidden flags. Use the cipher and pattern skills you brought with you
- 👀 Eye-Popping Demos - Moves that look like elite hacking, completely benign, designed to demystify what's actually happening behind the scenes
What Students Will Learn
Exponential Password Space
Why each added character is more than additive. The math behind every password meter you've seen.
Probability Intuition
How likely is a random guess? How many guesses until 50/50? The questions every security choice rests on.
Capture-the-Flag Mindset
Pre-built CTF puzzles teach the "find the gap" thinking that defines competitive cybersecurity.
Blue Team First
Understanding attacks to prevent them - the defender's perspective from the very first session.
Ethics First - Always
- Blue Team from the Start - We learn how attacks work to defend against them, not to use them
- No Real Targets - Every demo and CTF puzzle is pre-built and self-contained. Nothing on a live network or someone else's device
- Authorization Always - Even with skills, you only test systems you own or have explicit written permission to test
- The Pipeline to CyberPatriot - Cyber Sleuth feeds the same mindset that wins national CyberPatriot competitions
Why Schools Love This Workshop
- Real Cybersecurity Math - 7.G probability and 8.EE exponents come alive when applied to passwords
- CTF Practice - Direct prep for CyberPatriot, picoCTF, and similar competitions
- Demystifies Hacking - Students leave understanding that most real-world attacks are math, not magic
- Safe by Construction - No equipment of yours is touched; we bring everything self-contained
- Bridges to High School - Natural pipeline into Ethical Hacking Intro and CyberPatriot teams
Workshop Details
- Format: One-time workshop or recurring CTF series
- Duration: 2 hours
- Group Size: Up to 15 students
- Space Needed: Classroom with tables; projector helpful for the demos
- Equipment: All included - CTF puzzle packs, password math worksheets, demo gear
- Prerequisites: Comfort with multiplying multi-digit numbers and reading exponents
Perfect For
- Middle School Math Enrichment - 7.G probability and 8.EE exponents in cybersecurity context
- CyberPatriot Pipeline - The middle school stepping stone into competitive cyber
- Cyber Clubs - Recurring CTF series keeps a club running for a full semester
- STEM Days - The "looks like hacking" hook draws kids who otherwise wouldn't sign up for math
What's Included
- Pre-built CTF puzzle packs
- Password math worksheets
- Probability scenario cards
- Demo gear (all self-contained)
- Pipeline guide for CyberPatriot prep